Introduction:
Operational resilience is vital for financial institutions to navigate challenges, mitigate risks, and ensure business continuity. The EU Digital Operational Resilience Act (DORA) provides a comprehensive framework to enhance operational resilience in the financial sector. Implementing DORA requires a strategic audits and assessments, and staying updated on emerging threats and industry trends.
is vital for financial institutions to navigate challenges, mitigate risks, and ensure business continuity. The EU Digital Operational Resilience Act (DORA) provides a comprehensive framework to enhance operational resilience in the financial sector. Implementing DORA requires a strategic audits and assessments, and staying updated on emerging threats and industry trends.
Fostering a Culture of Resilience:
Leadership Commitment:
Secure  commitment from senior leadership to drive a culture of resilience and allocate necessary resources.
commitment from senior leadership to drive a culture of resilience and allocate necessary resources.
Employee Awareness:
Educate employees about the importance of operational resilience and their role in maintaining it.
Training and Education:
Provide training programs and workshops to build awareness and develop necessary skills for resilience.
Embed Resilience in Decision-making:
Integrate resilience considerations into day-to-day decision-making processes at all levels of the organization.
Promoting Collaboration Across Departments:
Cross-functional Teams:
Establish cross-functional teams to promote collaboration and information sharing.
Integrated Planning:
Foster collaboration  in the development and testing of business continuity plans and incident response procedures.
in the development and testing of business continuity plans and incident response procedures.
Communication Channels:
Implement effective communication channels to ensure seamless information flow during disruptions.
Joint Exercises and Simulations:
Conduct joint exercises and simulations involving different departments to enhance coordination and response capabilities.
Investing in Technologies:
Robust Infrastructure:
Invest in resilient and scalable technology infrastructure to support critical business functions.
Automation and Monitoring Tools:
Leverage automation and  monitoring tools for real-time risk assessment, incident detection, and response.
monitoring tools for real-time risk assessment, incident detection, and response.
Cybersecurity Measures:
Implement advanced cybersecurity technologies and practices to protect against evolving cyber threats.
Cloud Computing:
Embrace cloud-based solutions for data storage, backup, and recovery to enhance operational flexibility and resilience.
Conducting Regular Audits and Assessments:
Risk Assessments:
Conduct regular risk assessments to identify potential threats, vulnerabilities, and their potential impact.
Business Continuity Plan Testing:
Regularly test and update  business continuity plans to ensure their effectiveness during disruptions.
business continuity plans to ensure their effectiveness during disruptions.
Incident Response Preparedness:
Conduct regular drills and exercises to test incident response plans and improve response capabilities.
Compliance Audits:
Perform regular audits to ensure compliance with DORA regulations and industry standards.
Staying Updated on Emerging Threats and Industry Trends:
Continuous Monitoring:
Stay informed about emerging threats, vulnerabilities, and industry trends through continuous monitoring.
Threat Intelligence Sharing:
Engage with industry networks and share threat intelligence to stay ahead of evolving risks.
Regulatory Compliance:
Stay updated on regulatory guidelines, standards, and changes in DORA requirements to ensure ongoing compliance.
Professional Development:
Invest in training and development programs to enhance knowledge and skills related to operational resilience.
Conclusion:
Implementing best practices  in line with DORA is crucial for financial institutions seeking to enhance operational resilience. By fostering a culture of resilience, promoting collaboration, investing in technologies, conducting regular audits, and staying updated on emerging threats, financial institutions can build robust operational resilience frameworks. Implementing DORA not only ensures compliance but also helps institutions thrive in an ever-evolving landscape, safeguarding critical business functions and maintaining continuity even in the face of disruptions.
in line with DORA is crucial for financial institutions seeking to enhance operational resilience. By fostering a culture of resilience, promoting collaboration, investing in technologies, conducting regular audits, and staying updated on emerging threats, financial institutions can build robust operational resilience frameworks. Implementing DORA not only ensures compliance but also helps institutions thrive in an ever-evolving landscape, safeguarding critical business functions and maintaining continuity even in the face of disruptions.



 including technical failures, cyber-attacks, software glitches, human errors, natural disasters, or external threats.
including technical failures, cyber-attacks, software glitches, human errors, natural disasters, or external threats.  Exploring the potential regulatory consequences and financial penalties resulting from non-compliance with data protection and cybersecurity regulations.
Exploring the potential regulatory consequences and financial penalties resulting from non-compliance with data protection and cybersecurity regulations. brand value resulting from negativemedia coverage, public perception, and loss of competitive advantage.
brand value resulting from negativemedia coverage, public perception, and loss of competitive advantage. Discussing the benefits of robust business continuity strategies, including backup systems, disaster recovery plans, and alternative service provisions to minimize financial disruptions.
Discussing the benefits of robust business continuity strategies, including backup systems, disaster recovery plans, and alternative service provisions to minimize financial disruptions.

 institutions need to follow a systematic approach. This includes conducting a comprehensive risk assessment to identify vulnerabilities, prioritizing critical business functions, setting impact tolerances, developing robust business continuity plans, and fulfilling compliance requirements such as regular testing, training, and reporting. Maintaining compliance involves ongoing monitoring, updating of policies and procedures, and adapting to evolving regulatory guidelines. By implementing these measures, financial institutions can ensure they meet DORA regulations, mitigate operational risks, and safeguard their business continuity in the face of disruptions.
institutions need to follow a systematic approach. This includes conducting a comprehensive risk assessment to identify vulnerabilities, prioritizing critical business functions, setting impact tolerances, developing robust business continuity plans, and fulfilling compliance requirements such as regular testing, training, and reporting. Maintaining compliance involves ongoing monitoring, updating of policies and procedures, and adapting to evolving regulatory guidelines. By implementing these measures, financial institutions can ensure they meet DORA regulations, mitigate operational risks, and safeguard their business continuity in the face of disruptions.
 we will provide a comprehensive guide on the steps involved in achieving compliance with DORA regulations.
we will provide a comprehensive guide on the steps involved in achieving compliance with DORA regulations.  all business functions and their dependencies within the organization.
all business functions and their dependencies within the organization.
 essential for navigating the implementation process effectively.
essential for navigating the implementation process effectively. outlines the key milestones, timelines, and responsibilities for each aspect of DORA implementation.
outlines the key milestones, timelines, and responsibilities for each aspect of DORA implementation. focusing on risk management, business continuity, incident response, and cybersecurity.
focusing on risk management, business continuity, incident response, and cybersecurity. infrastructure and identify any gaps or limitations in supporting DORA compliance.
infrastructure and identify any gaps or limitations in supporting DORA compliance.
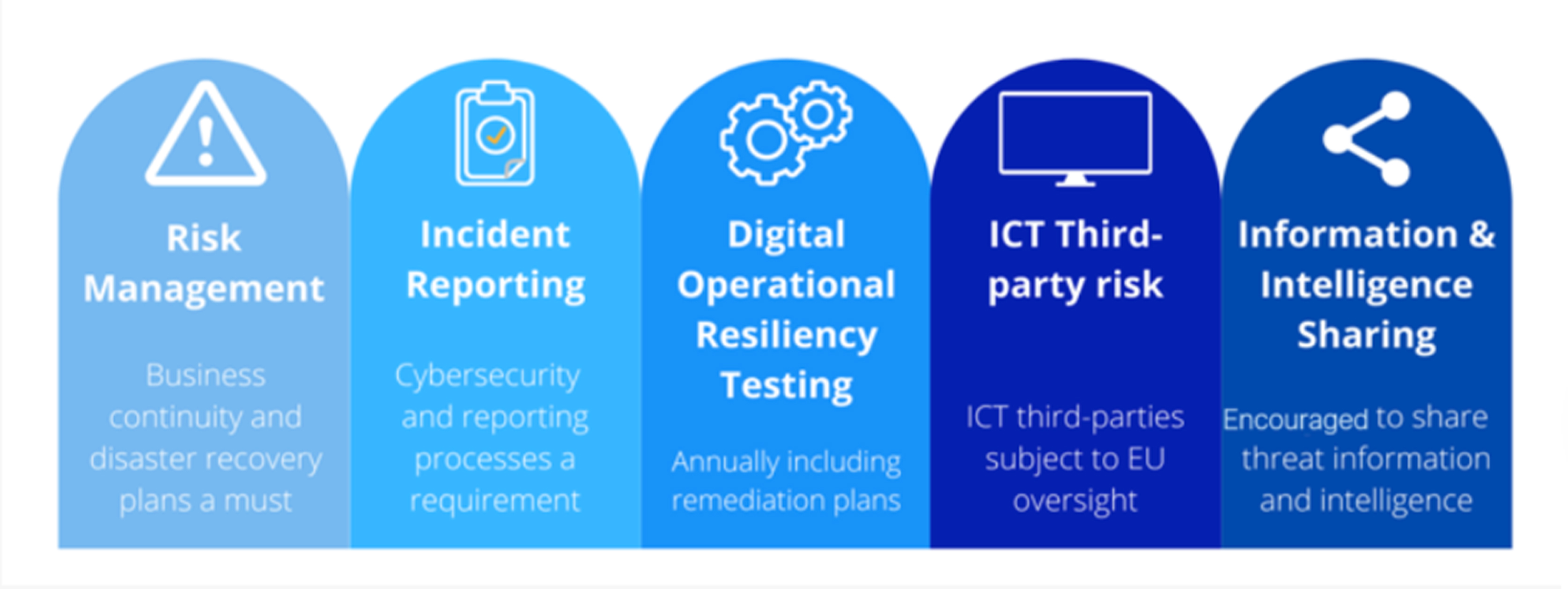

 The third pillar of DORA focuses on cyber resilience, acknowledging the increasing importance of protecting financial firms against cyber threats. To apply this pillar effectively, financial firms should:
The third pillar of DORA focuses on cyber resilience, acknowledging the increasing importance of protecting financial firms against cyber threats. To apply this pillar effectively, financial firms should:

 essential services. In response to the increasing frequency and
essential services. In response to the increasing frequency and disasters.
disasters. nancial entities to promptly report significant operational and security incidents to the relevant regulatory authorities.
nancial entities to promptly report significant operational and security incidents to the relevant regulatory authorities.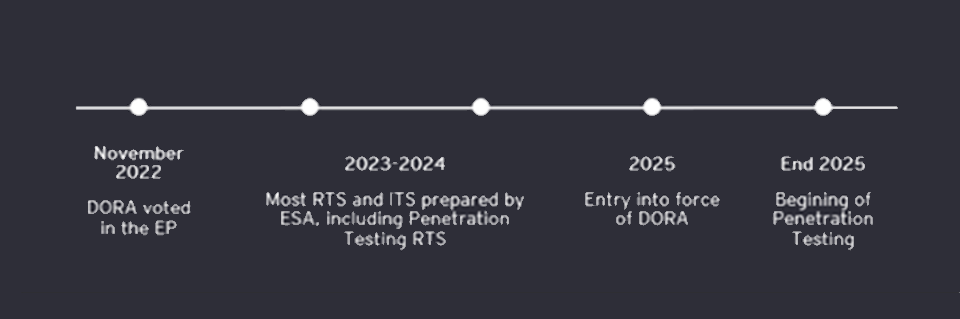


 maximum amount of disruption that the firm can tolerate without compromising the provision of the service. The impact tolerances should be based on the needs of customers and the broader financial system.
maximum amount of disruption that the firm can tolerate without compromising the provision of the service. The impact tolerances should be based on the needs of customers and the broader financial system. The plans should be regularly tested and updated to ensure their effectiveness.
The plans should be regularly tested and updated to ensure their effectiveness. of disruptions on their operations and outline the steps that they will take to ensure continuity of critical functions.
of disruptions on their operations and outline the steps that they will take to ensure continuity of critical functions.
 organizations with a more dynamic and proactive approach to risk management. By continuously monitoring the risk landscape in real-time, organizations can quickly identify and respond to potential risks and threats. This enables them to take preemptive action to minimize the impact of disruptions, rather than simply reacting after the fact.
organizations with a more dynamic and proactive approach to risk management. By continuously monitoring the risk landscape in real-time, organizations can quickly identify and respond to potential risks and threats. This enables them to take preemptive action to minimize the impact of disruptions, rather than simply reacting after the fact. landscape, organizations can identify potential threats before they occur, enabling them to take preemptive action to minimize the impact of disruptions.
landscape, organizations can identify potential threats before they occur, enabling them to take preemptive action to minimize the impact of disruptions. infectious diseases in real-time, enabling them to take preemptive action to prevent the spread of diseases and minimize the impact on patients.
infectious diseases in real-time, enabling them to take preemptive action to prevent the spread of diseases and minimize the impact on patients. identify the relevant data sources for their specific risk landscape.
identify the relevant data sources for their specific risk landscape.

 including risk management, business continuity planning, and disaster recovery. Operational resilience is focused on the specific processes and systems that are critical to the delivery of products and services, and encompasses all aspects of those processes and systems, including people, processes, and technology.
including risk management, business continuity planning, and disaster recovery. Operational resilience is focused on the specific processes and systems that are critical to the delivery of products and services, and encompasses all aspects of those processes and systems, including people, processes, and technology.