An unplanned IT failure or IT service interruption which is yet to pose a critical IT threat is an IT incident. The sudden IT incident event means key business operations are not continuing, affecting a large number of service areas and people. In this instance, near real-time, IT incident management built on Zapoj CEM provides innovative solutions with a plethora of tools- visual risk intelligence, reliable IT alerting to improve decision making and to proactively handle critical IT events in a high-growth and ever-expanding learning environments like colleges and universities.
The CEM technology that Zapoj leverages uses AI-powered solutions to analyze the complexity of IT events, improve visualization with data integration capabilities and enable actions through apps, desktop software for incident responders. The quick actions can deliver faster resolutions to better reinstate IT services and mitigate its impact on operations that college campuses build their interdependencies upon for teamwork and communications.
Here’s what IT outages mean to colleges and universities and how Zapoj as a leading CEM software can help them boost the efficiency of their IT Service Management tool to provide a fantastic experience for staff, faculty, and students.
What system outage costs your higher education?
IT services are the benchmark to ensure uninterrupted learning, research and development, and the undertaking of official communications and consulting services all through the day, year over year. University administrators, faculty, and staff need a wide range of IT tools that allow them to connect and communicate with students, parents, visitors, stakeholders, and peers. Crucial administrative operations from building a virtual network for distance learning to offering rapid and ceaseless online course registration- a robust IT service extends its support for user satisfaction, unique experience, and efficiency to help foster an advanced learning environment on a higher level.
year. University administrators, faculty, and staff need a wide range of IT tools that allow them to connect and communicate with students, parents, visitors, stakeholders, and peers. Crucial administrative operations from building a virtual network for distance learning to offering rapid and ceaseless online course registration- a robust IT service extends its support for user satisfaction, unique experience, and efficiency to help foster an advanced learning environment on a higher level.
The complexities as exacerbated by sudden application downtime, website crash, power outage, low performances of data centers, networks, and high-risk cyber-attacks can heighten the risks of service disruption.
IT downtimes basically are the consequences due to critical events like heavy rains, storms, lighting, and mostly because of unforeseen developments across IT services that appear suddenly as major threats for higher education.
| IT downtime insights:
As reported by Gartner, IT downtime costs businesses 5,600 USD per minute. A more recent report highlights that an estimated $260,000 gets wasted due to an average downtime per hour. The study reported the degradation by 60% in monetary losses since 2016 across businesses. |
Higher education faces modern-day IT outages which impact its ability to deliver service across channels, large spanning departments, and leave little room for IT responders to prevent chaos and troubles.
The routine IT challenges in higher education across universities and college campuses can subside when education administrators or the IT service management team rely on visualization and comprehensive IT alerting responses.
Ensure rapid recovery by optimizing Zapoj CEM IT incident management
AI-powered IT incident handling tool builds situational awareness across the IT Service Management and helps with event identification, prioritization, and remediation as a form of the initial restoration process. The IT support team in your college campus can establish a unified network that escalates real-time alerting and helps reduce the impact.
the initial restoration process. The IT support team in your college campus can establish a unified network that escalates real-time alerting and helps reduce the impact.
Route incidents with predictive intelligence
The incident routing is still inconvenient for several academic infrastructures as it relies upon manual workflow processes. The worst part is that it wastes valuable time for recovery and does notprovide much progress within scheduled work hours for IT service desk staff. And in parallel, manual handling of workflow is error-prone, and hence routing is more likely to reach the wrong destination, delaying the recovery process.
With predictive intelligence at the core of Zapoj IT incident management, the CEM tool can harness data from multiple existing ITSM solutions, Service desk, IT monitoring tools, and IT alerting tools. By analyzing risk data, Zapoj improves visibility into evolving IT threats and helps route incident handling workflows in an automated way.
Apply IT alerting or IT incident communications
An easy-to-use command center is competent in improving visibility into your workflows. You can use predefined message templates to communicate with IT service desk staff and  prioritize incident handling response by creating chatOps and war rooms. Relying on efficient IT alerting or IT incident communication tools, you can discuss with your response team and derive actionable insights into the next step of the recovery process.
prioritize incident handling response by creating chatOps and war rooms. Relying on efficient IT alerting or IT incident communication tools, you can discuss with your response team and derive actionable insights into the next step of the recovery process.
Communicate IT issues with on-call management
Zapoj always makes sure your on-call team is ready to solve the IT issues as soon as the issue is escalated. As you build escalation rules, on-call schedule management is much easier. So, the IT incident team is always confident that the right response team does not miss a critical alert until acknowledged and addresses the issues.
The efficiency of delivering real-time IT incident response improves the mean time to repair (MTTR) and encourages faster resolutions of the IT incident.
Advanced reporting and analytics
Zapoj also carefully designs its analytics dashboard to help the IT response team to assess how they perform during IT incidents. In-depth analysis of team response by area and type help meet service-level expectations. From this perspective, incidents that take too long to handle can be resolved using performance analytics.
perspective, incidents that take too long to handle can be resolved using performance analytics.
Institutes are looking for more effective IT service tools to provide uninterrupted service to advance their learning and knowledge. Zapoj delivers high-caliber support to mission-critical objectives of higher education learning management and also improves ROI by automating IT alerting. In times of pandemic where virtual learning rests on the active and robust IT infrastructure, embedding Zapoj CEM into your ITSM systems enables higher education to deliver a connected experience for students, faculty, and staff. To support your growth and transform the academic experience, Zapoj CEM must feature in your IT infrastructure. Call us for a demo.




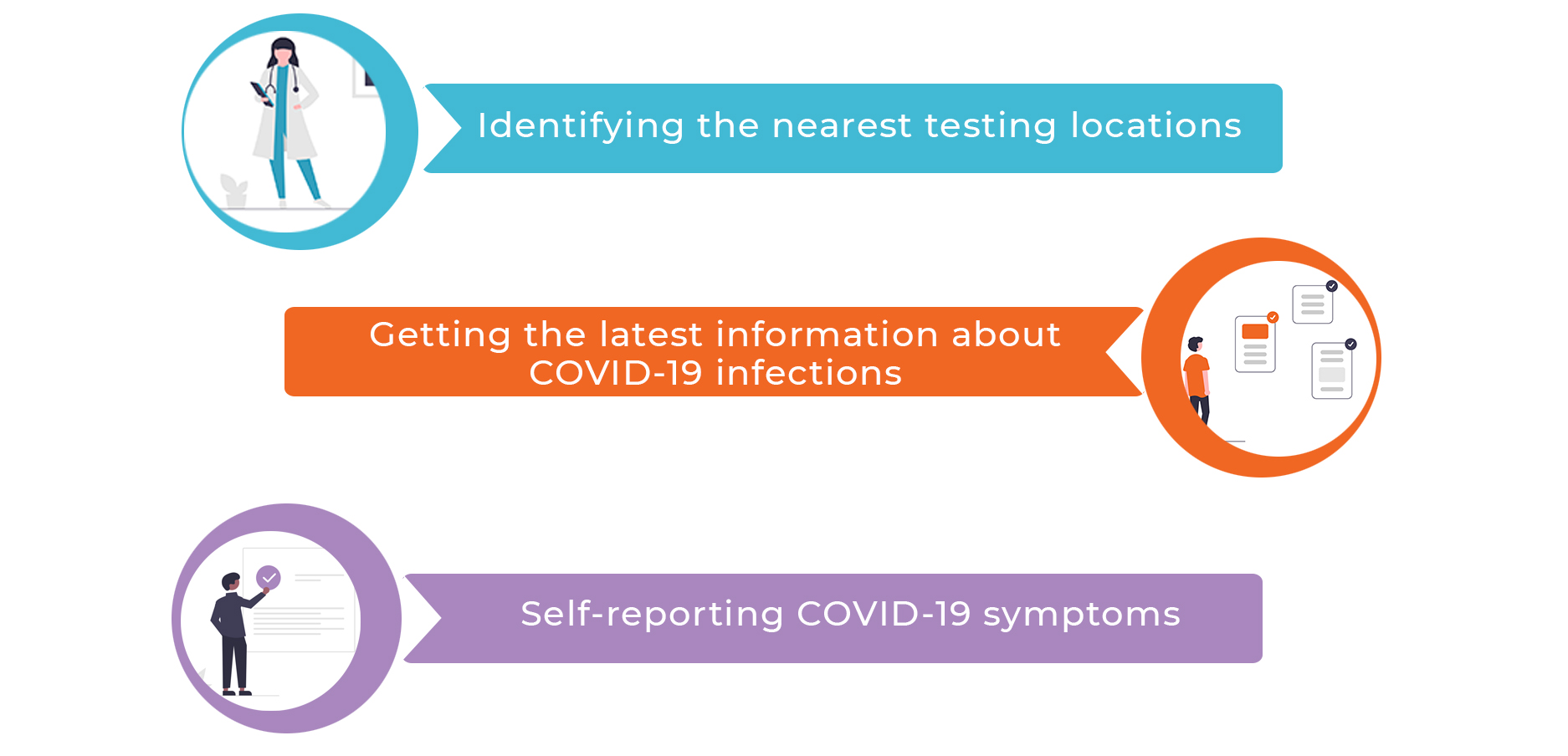
 significant criteria of disease control. Using location intelligence technology, Zapoj empowers facility managers to fully utilize its geospatial mapping solutions to quickly identify the risk-prone zones inside the premises of the campus or within a particular space such as library, office, administrative departments, and anywhere in the university.
significant criteria of disease control. Using location intelligence technology, Zapoj empowers facility managers to fully utilize its geospatial mapping solutions to quickly identify the risk-prone zones inside the premises of the campus or within a particular space such as library, office, administrative departments, and anywhere in the university. institutions may need this approach to amp up their campus readiness. Enrolling campus members, staff, faculty, and students in the vaccination is readily available with Zapoj contact tracing capabilities. As members sign up for opt-in services, they can communicate their current status after vaccination and receive reminders for the next dose of vaccine. By having everyone in the contact centers, administrators can keep track of vaccine status and ensure wellness checks.
institutions may need this approach to amp up their campus readiness. Enrolling campus members, staff, faculty, and students in the vaccination is readily available with Zapoj contact tracing capabilities. As members sign up for opt-in services, they can communicate their current status after vaccination and receive reminders for the next dose of vaccine. By having everyone in the contact centers, administrators can keep track of vaccine status and ensure wellness checks.